This procedure work in Horizon Workspace 1.8! ![]()
One of the very cool features Horizon Workspace , is the possibility of deposition of applications such as the “web”. These are generally nested redirection to external sites, using the opportunity to combine authentication mechanism through the use of SAML / SSO. SAML (Security Assertion Markup Language) is a transport protocol which mediates the authentication of users (and transmission of information about user permissions between systems). So, more human language, a user logs in only to Horizon Workspace (AD domain where the station is installed on the client, this is done automatically), then “click” in application “vCloud” and is transferred automatically logged into your Organization (with appropriate permissions). Benefit from the use of SSO is known, is always less than the number of windows login / password to overcome. Benefit second, the exposure to the world of a single portal (eg for remote workers or those with BYOD internally) with a set of properly prepared “redirects” (and the rest of ThinApp’uff).
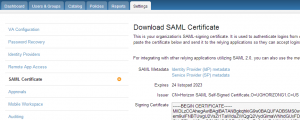
Preparation of such a WebApp is very simple , in a first step we charge an XML file containing the appropriate Identity Provider metadata. After logging into the Horizon Workspace as an administrator, all the necessary links are in the Settings -> SAML Certificate (or direct address https://horizon_server/SAAS/API/1.0/GET/metadata/idp.xml ):
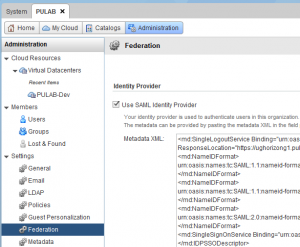
In the next step, log on as an administrator or organizational system to vCloud Director and proper configuration of the Organization “, click” Settings-> Federation, select the “Use of SAML Identity Provider” and the window below paste the XML file containing our metadata (idp.xml).
Then we have to download the vCloud Director XML file with the appropriate SSL certificate (the certificate is unfortunately one-so best to “regenerate” before downloading (available in the same section “Federation”)). The file is available at https://vcloud_server/cloud/org/MOJAORGANIZACJA/saml/metadata/alias/vcd (saving should add the xml extension). But beware, the certificate is common to all processes SAML, when expires or is changing, we need to reconfigure all our WebApp (paste again changed xml).
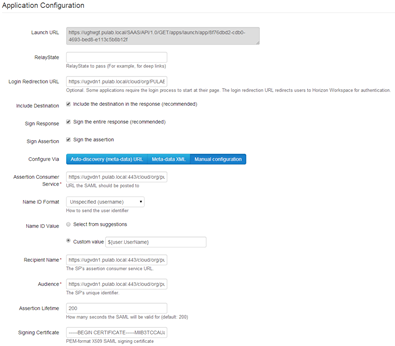
Finally, log in again to the Horizon Workspace as an administrator, enter the Catalog -> Web Applications and click the “create a new one.” We are preparing an application profile as shown below (the contents of the downloaded file vcd.xml paste in a Meta-Data XML):
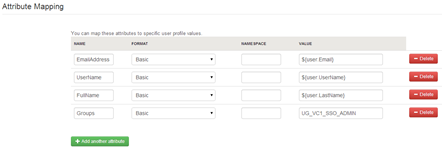
We also need to manually add attributes mapping of users (compared to version 1.0 there is a change, you must manually add the attribute group, traced with Tomas Fojty ):
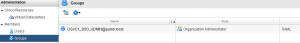
The final step is to add users to our organization or group (mapped above). But beware, we use the SAML authentication type, by importing a group we have to choose SAML (not LDAP) and manually enter the correct group:
And finally we can enjoy our app :)
SAML is a universal solution, we can use it to embed a WebApp any of our sites or applications.
Was this information is helpful? Tell me, please leave a comment!